Automated address poisoning campaigns target millions of Ethereum wallets, using dust transfers and fake tokens to insert spoofed addresses.
Ethereum users are facing a growing wave of address poisoning attacks as scammers scale the tactic through automation. Recent blockchain data suggests the activity has shifted from occasional spam into organized campaigns targeting thousands of wallets. Attackers rely on deception rather than direct wallet breaches. Even with a very low success rate, the strategy remains profitable because of the high volume of attempts.
Etherscan Alerts Reveal Surge in Ethereum Address Poisoning Attempts
Concerns resurfaced after an Ethereum user known as Nima reported unusual activity following two stablecoin transfers. Within about 30 minutes of the transactions, the user received more than 89 address watch notifications from Etherscan. Each alert was triggered by a poison transfer sent to the wallet. The goal was to insert lookalike addresses into the wallet’s transaction history.
Address poisoning attacks are getting out of hand. I just sent two stablecoin transactions and received +89 emails from my Etherscan address watch alert notifications.
It took them <30 mins to create all of these on mainnet.
So many will fall victim to this. pic.twitter.com/H1nGaMMprE
— Nima 👁️ (@0xNimaRa) February 13, 2026
Address poisoning relies on the simple manipulation of user behavior. Attackers create wallet addresses that resemble legitimate ones previously used by the target. These fake addresses mimic the first and last characters of the real address. Once the spoofed address is generated, a small transaction is sent to the victim’s wallet.
As a result, the fake address appears in the transaction list alongside legitimate transfers. Many users later copy addresses from past transactions when sending funds. If a poisoned address appears there, funds can be mistakenly sent to the attacker.
Attackers Use Dust Transfers and Spoofed Tokens to Trick Users
Research indicates that the scale of these campaigns has expanded significantly. A 2025 study examining activity between July 2022 and June 2024 recorded roughly 17 million poisoning attempts. About 1.3 million Ethereum users were targeted during that period. Confirmed financial losses reached at least $79.3 million.
In parallel, competition among attackers has intensified. Multiple attackers often target the same wallet shortly after a legitimate transaction occurs. Each attempts to place their spoofed address into the victim’s transaction history before the others. The attacker who appears first increases the likelihood that the fake address will later be copied.
Several techniques commonly appear in these campaigns:
- Dust transfers: Attackers send tiny token amounts so the fake address appears in transaction history.
- Zero-value transfers: Transactions with no value are used solely to place spoofed addresses into wallet records.
- Spoofed token transfers: Fake tokens imitate assets that the victim previously transferred.
- Automated monitoring systems: Bots scan blockchain activity and target wallets immediately after transactions occur.
From an economic perspective, the strategy functions as a high-volume probability model. Researchers estimate that a single poisoning attempt succeeds only about 0.01% of the time. In practical terms, roughly one in every 10,000 poison transfers results in a mistaken payment.
However, large-scale campaigns offset the low success rate. Attackers often send thousands or even millions of poison transfers across the network. A single successful transfer involving a large amount can cover the cost of many failed attempts.
A widely discussed case in December 2025 illustrates the potential impact. One victim reportedly lost $50 million after sending Ethereum to a poisoned address copied from the transaction history.
Ethereum’s Lower Transaction Costs Coincide With Surge in Suspicious Dust Transfers
Network upgrades have also played a role in recent activity trends. Ethereum’s Fusaka upgrade, activated on December 3, 2025, reduced transaction costs and improved scalability. While the upgrade benefits normal users, lower fees also reduce the cost of mass poisoning campaigns.
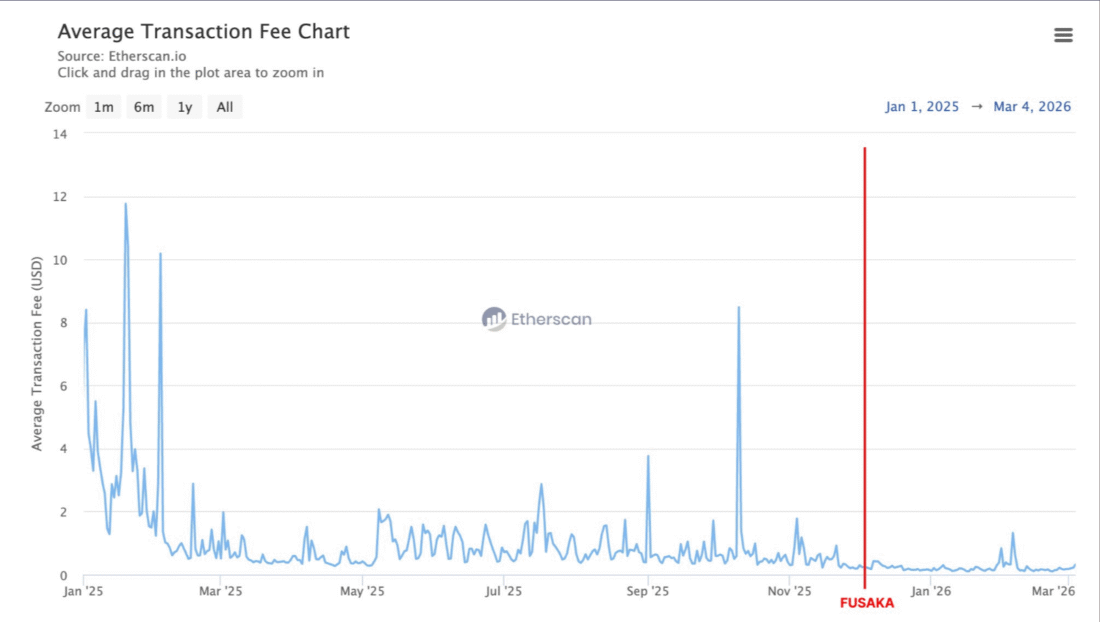
Image Source: Etherscan
Following the upgrade, network activity increased noticeably. Ethereum processed about 30% more transactions per day during the following 90 days. At the same time, the number of new addresses created each day rose by roughly 78%.
Dust transfer activity rose sharply during the same period. USDT dust transfers increased from 4.2 million to 29.9 million. USDC dust transfers climbed from 2.6 million to 14.9 million, while DAI dust transfers rose from about 142,000 to more than 811,000.
Not every dust transfer represents a poisoning attempt. Small transfers can occur during routine trading activity or token swaps. Even so, clusters of dust transactions often point to coordinated poisoning campaigns.
Security analysts continue to stress a simple precaution. Wallet addresses should always be verified manually before sending funds. Copying addresses directly from transaction history remains one of the most common ways users fall victim to address poisoning scams.