The advent of darknets, along with the popularization of cryptocurrencies, namely bitcoin, have helped hackers market their services, throughout the past few years, via means that keeps them undetected and untraceable by law enforcement agencies.
Why is the Darknet Perfect for Hackers Who Want To Market Their Services?
Darknet websites can only be accessible via networks such as Tor and I2P. Tor only accessible hidden web services can be identified by the domain suffix “.onion”. Even though Tor is centered upon providing users anonymous access to the internet, it also allows users to host their websites in an anonymous manners. Thanks to Tor’s layered encryption protocol, the identity and location of a darknet user will always remain anonymous and untraceable.
A study conducted in 2014, by Gareth Owen, University of Portsmouth, revealed that the most commonly accessed content on the Tor network was related to child pornography and black markets. However, the Tor sites with highest traffic flows were linked to botnet operations and Command & Control (C&C) servers.
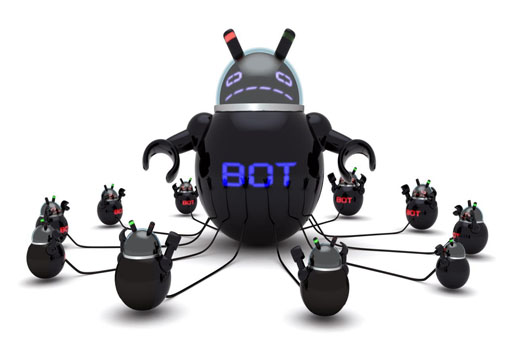
Botnets:
Enormous computer networks that are comprised of infected machines, which are referred to as botnets, are presently the most disastrous threat for the global digital security. Botnets are a group of smart tools for launching huge distributed denial of service attacks, spreading spam and phishing emails, spreading ransomware, phishing private information in an attempt to steal money from various online banking services.
Nowadays, hackers’ can turn almost any form of digital device connected to the internet into botnets complying to their orders including PCs with Windows operating systems, Android smartphones and IoT devices that have public IP addresses e.g. HDTV cameras, LED screens…etc. Today, there are multiple ways to hire a botnet network on the darknet especially on the Tor network. You can now hire a botnet network, buy a botnet builder kit and almost any other hacking service in a peer-to-peer, or rather a hacker-to-hacker manner. The simplest way to create a botnet network is to create a central server, hosted on a Tor hidden service, for spreading of commands and the creation of clients, i.e. enslaving machines to become bots on the network, that will connect to the server to follow the orders of the C&C server. These forms of botnets are known as “traditional bots”.
Many black markets on the Tor network today have a section for hacking services and tools. You can now hire a hacker on many of the P2P marketplaces on Tor including Alphabay, Dream Market, Valhalla, House of Lions and Tochka. There are also websites that are setup by hackers to sell directly their services to the clients, yet these websites are not recommended; it is better to use P2P marketplaces that include a feedback or a review system to help eliminate fraudulent sellers.
Image from Flickr