Creators of “WannaCry”, a new form of ransomware, managed to only make around $50,000 worth of bitcoins via infecting and encrypting the files on around 200,000 PCs all over the world, according to CNBC’s industry sources.
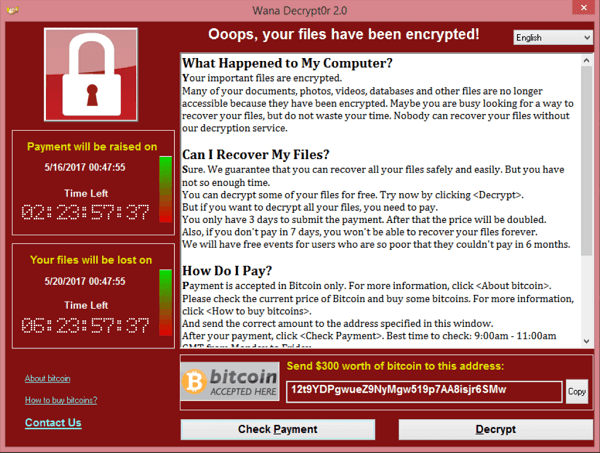
Last Friday, WannaCry managed to infect PCs, running Widows’ OSs, across more than 150 countries all over the world. $300 worth of bitcoin were demanded as a “ransom” to decrypt the files of every infected machine. According to James Smith, Elliptic’s CEO, approximately $50,000 worth of bitcoin were paid to hackers by victims of the ransomware by 7 am EST today.
WannaCry is formulated to ask for a ransom of $300 in the beginning, which would rise to $600, if the victim refuses to pay the ransom during the first 7 days following infection of his/her machine. Accordingly, experts predict the amounts paid to the creators of WannaCry to increase after a few days, when the 7 day deadline is due. Given the wide scale and global nature of the attack, the amount of coins paid to the hackers is still relatively low. Law enforcement agencies and network security professionals have been urging victims of WannaCry not to pay the ransom.
Payments from victims of the ransomware were sent to three bitcoin addresses, according to James Smith, yet the hackers still did not move any of the coins they received to any other addresses.
What is WannaCry Ransomware?
WannaCry, which is also known as WannaCrypt, Wanna Decryptor and WanaCrypt0r 2.0, is a novel ransomware that targets machines running Microsoft Windows operating systems. WannaCry spreads via multiple means such as phishing emails, and it also spreads as a computer worm on unpatched systems.
The attack affected individuals as well as big companies. Many companies in Spain were affected including Telefonica. The UK’s National Health Service (NHS) was hit hard by WannaCry. Other affected companies include FedEx, LATAM Airlines and Deutsche Bahn.
A couple of days after the attack was launched, a security expert discovered an efficient kill switch, which shielded unaffected machines against new infections, provided that their systems were patched. This led to slowing down of the spread of the ransomware. Security professionals have warned against a second attack wave, as new versions of the ransomware were detected lacking the “kill switch”.