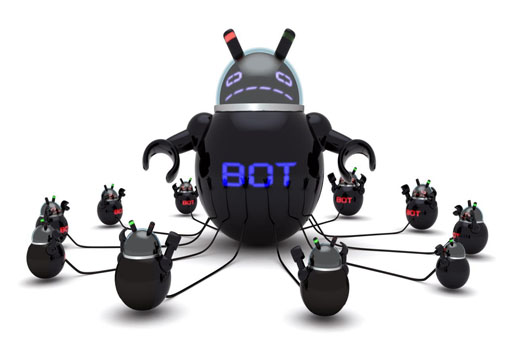
A new botnet has made its way onto Android phones by exploiting a loop that allows it to mine cryptocurrency.
Botnet Takes Crypto While Offering No Rewards
This is basically a form of crypto-jacking, a new type of security breach that allows hackers to take control of one’s computer or digital device to mine crypto. Typically, Monero is the subject of the hackers’ attention given its quasi-anonymous properties. All the while, a user has no idea that their device has been taken over, and they have not given their permission for the device to be used for mining purposes.
That doesn’t mean much to the hackers, unfortunately, who utilize the energy of a device to extract new coins and rake in a massive profit. Sadly, the original user of the device receives nothing from the hackers’ efforts unless you count the expensive energy bills they are likely to garner each month. It’s a sad and unfair sight in many ways, and one that seems to be spreading rapidly throughout the cryptocurrency arena.
The botnet was discovered by cybersecurity firm Trend Micro, who says that it has spread to approximately 21 countries at press time and is most active in South Korea.
Trend Micro has issued the following statement about the botnet:
Any system that has connected to the original victim being attacked via SSH is likely to have been listed as a ‘known’ device on its operating system. Being a known device means the two systems can communicate with each other without any further authentication after the initial key exchange. Each system considers the other as safe. The presence of a spreading mechanism may mean that this malware can abuse the widely used process of making SSH connections.
The botnet works by abusing open ADB ports on Android phones. These ports are available on all Android devices, though for the most part, many do not ship to customers with these ports enabled. However, the few that do are at risk, as open ADB parts do not require authentication as a “default setting.” This allows the botnet to step in and spread from the devices to all other acquainted networks through SSH connections.
This Leads to a Bigger Problem…
The botnet then performs a series of scans on the host item and on all connected networks and issues a command, allowing its malware to be downloaded to a target system. Permission settings are ultimately disposed of, along with any evidence that suggests the malware’s presence.
The problem surrounding malware of this nature is that it is allegedly becoming more common. The recent shutdown of Outlaw and similar systems designed to infiltrate, or attack computer networks is always a positive step, but their presence disavows the legitimacy that the crypto space is consistently working to establish.